Cybercriminal Lazarus group hacked Bangladesh Bank
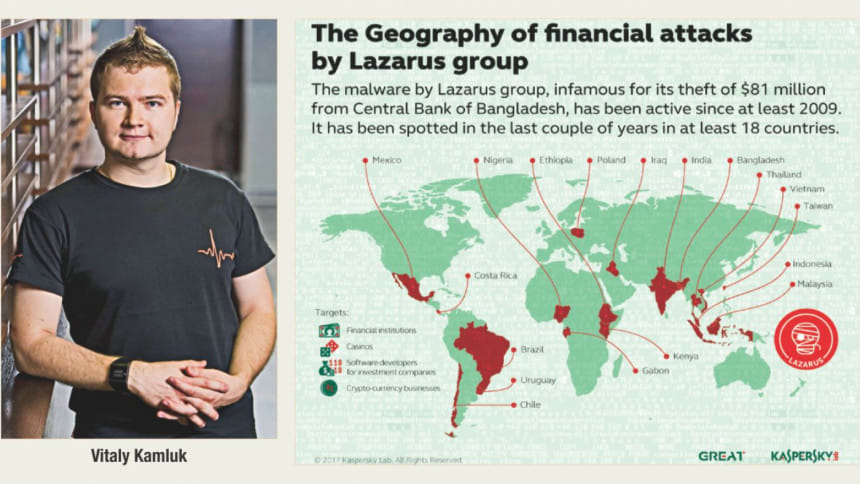
Cybercriminal gang Lazarus group carried out the $81 million Bangladesh Bank cyber heist, not the other groups named since the February 2016 incident, according to a top researcher of cyber security firm Kaspersky Lab.
Vitaly Kamluk, director of the Moscow-based company's global research and analysis team for the Asia Pacific region, said: "We're pretty sure it was the work of Lazarus group."
The researcher made the remarks in an email interview with The Daily Star recently.
By contrast Lamont Siller, an FBI officer in the Philippines involved in the investigations, said last month that the heist from the central bank's account at the New York Federal Reserve was "state-sponsored".
In the wake of the crime, then central bank governor Atiur Rahman was forced to step down along with two deputies. BB formed a committee to probe the attacks but the report has not been made public yet.
On 3 April this year Kaspersky Lab released a 58-page report on Lazarus Group, the gang behind some of the most notable cybercrimes in recent times. The report said the BB heist may very well have been their work.
When asked whether the heist was state-sponsored, Kamluk said: "We don't do attribution, we publish only the facts."
However, he said Lazarus has been known for sophisticated cyber espionage since 2009. "Running such campaigns requires vast human and financial resources which very few cybercriminal groups possess. Most probably this isn't just a cybercriminal group."
After the BB heist came into the spotlight, Kaspersky Lab started to search for new Lazarus malware samples and successfully identified a chain of infections, according to Kamluk.
"Then we conducted several incident response operations in Southeast Asia and Europe aimed at preventing additional attempts to steal money."
He said in parallel with an attack against Bangladesh, Lazarus was preparing to conduct similar operations on other banks.
The Kaspersky Lab report suggests that a North Korean IP address was involved. Kamluk said it could mean several things: the attackers connected from that IP address; it was a carefully planned false flag; or someone in North Korea accidentally visited the command and control URL.
About any weakness or negligence on the part of the BB, SWIFT or New York Fed, Kamluk said: "We note that in all of the attacks against banks we have analysed, SWIFT software solutions running on banks' servers have not demonstrated specific vulnerability. The attacks were focused on banking infrastructure and staff, exploiting vulnerabilities in commonly used software or websites, brute forcing passwords, using keyloggers and elevating privileges."
The way banks use SWIFT software requires personnel responsible for administration and operation. Sooner or later, the attackers find the personnel and gain the necessary privileges to access the SWIFT platform, Kamluk said.
"With administrative access they can manipulate the software as they wish. There isn't much to stop them because from a technical perspective their activities may not differ from what an authorised engineer would do: starting and stopping services, patching software, modifying the database."
"In all the breaches we analysed, SWIFT hasn't been directly at fault. More than that, we have witnessed SWIFT implementing integrity issue detection to protect customers."
When asked whether the report could be used as legal evidence, Kamluk said Kaspersky Lab didn't aim to create a report to fit legal requirements.
"Our goal was to protect our customers. Although we do forensic analysis in a way that is very similar to the best law enforcement standards, we are not obliged to follow the full chain of custody. However, on request we can."
Talking about the heist's impact on the local IT industry, Prabeer Sarker, chief executive officer of Officextracts which is the Bangladesh Kaspersky Lab distributor, said it had implications not only for IT but also for the financial, government and corporate sectors, as well as the entire nation.
"All quarters became aware of cyber security with a jolt. The major effect is awareness."
He said immediately following the incident the number of people and establishments claiming cyber security expertise mushroomed, with many using the incident to generate hit and run business. "That phase is fading now. IT professionals have gained experience over the past year to implement the right security strategies."

 For all latest news, follow The Daily Star's Google News channel.
For all latest news, follow The Daily Star's Google News channel. 



Comments