Sophisticated tools used for hacking
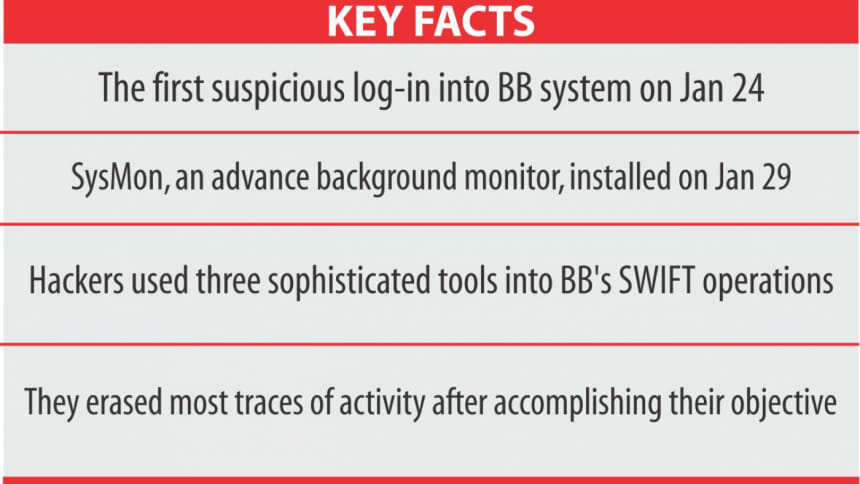
The hackers, who stole $101 million from Bangladesh Bank's reserves, used advanced tools to break into its payment systems, harvested credentials and erased most traces of activity after accomplishing their task.
Along with using malicious software, the perpetrators, who are yet to be identified, deployed three sophisticated tools into the central bank's SWIFT operations, according to an interim probe report submitted on March 16.
The hackers installed keyloggers to steal passwords by monitoring keyboard activities and attacker utilities to maximise their chances of success.
In addition, at least 32 other computers of the BB network were hacked, in an attempt to steal about $1 billion out of the central bank's reserves with the New York Fed on the night of February 4, according to the interim report of US-based FireEye and World Informatix Cyber Security.
The first suspicious log-in came on January 24. Five days later, on a quiet Friday (January 29), the attacker installed SysMon, an advanced background monitor, in SWIFTLIVE and left it running for a full day.
SWIFTLIVE is the main platform of the BB using which it issues international payment orders. SysMon is a background service that logs security-related process and network activity to the Windows event log.
After that the attacker dumped the contents of the SysMon event logs which experts interpret as reconnaissance activity, meaning the attacker aimed to gather critical information like credentials from the command line used in any of the running processes or programmes.
Analysis shows, the attacker forgot to delete the SysMon log files at least for one day, which enabled investigators to retrieve very valuable information.
On both SWIFT platforms known as SWIFTLIVE and SWIFTUAT, the attackers appear to be operating exclusively from the very beginning with local administrator accounts, according to the report.
Cyber security companies FireEye and World Informatix that have prepared the report have gathered substantive evidence to confirm that the unauthorised payments were made as part of a sophisticated and targeted attack on its system.
The malware was specifically designed to bypass certain security measures and operate on SWIFT Alliance Access servers.
SWIFT messaging system is based in Belgium and banks around the world use it for secure financial communication.
In the BB's IT infrastructure, complex malwares have been identified with advanced features of command and control communication, harvesting of credentials and to securely erase all traces of activity after the transfer orders were sent.
PATH TO BB'S SWIFT SYSTEMS
A central bank official said the linking of the BB's SWIFT operation with the central bank's whole IT operations in Dhaka and other cities in October last year through the launch of the real-time gross settlement (RTGS) system might also have given the hackers a path to break into the BB's SWIFT platform.
Earlier, the SWIFT operations and the central bank's IT operations were separate.
The RTGS was introduced to bring all banks and their branches under one umbrella. So far, only three local banks have joined the platform while others are still using an alternative one.
But the BB's SWIFT system was weakened as the linking to the RTGS was done without installing a strong firewall, said officials.
OTHER COMPUTERS HACKED
The 32 computers, which were also hacked into, were used to gain control of the SWIFT servers and related desktop computers, according to the interim report seen by The Daily Star.
The number of computers used to hack the BB system is expected to grow, as investigators are continuing to sweep all corporate assets and discovering additional information. The investigation, said to be at a critical stage, will continue for about two more weeks.
The security breach of the SWIFT environment is part of a much larger breach that is currently under investigation, according to the report.
WHO ARE THE HACKERS?
The hackers have not been identified yet, but FireEye is currently tracking this cluster of activity as an “uncategorised” threat group, which is a suspected financially motivated group, also known as FIN group.
“An uncategorised group is a cluster of activity in which we have not yet formally attributed the threat to a specific advanced persistent threat (APT) or financially motivated group (FIN),” the report said.
FireEye Intelligence has observed APT groups, cyber-crime groups as well as hacktivists target the financial industry.
APT groups primarily collect information that can provide insight into a targeted company's operation or into its sensitive customers. Cybercriminals or FIN groups attempt to seek out account data and other data that can be monetised.
FireEye, according to the probe report, has observed these same suspected FIN threat actors within other customer networks in the financial industry, where these threat actors appear to be financially motivated, and well-organised.
The actors have not been known to be destructive in nature, but seem to follow a general APT style methodology: gain access to the network, utilising legitimate access and stolen credentials to spread malware across the network.
The group generally installs tools such as screen scrapers, keyloggers, passive backdoors, and a proxy aware backdoor to identify application processes to exploit or learn business processes that would aid the attacker in achieving their objectives.
Once the actors have completed their objectives within a victim network, FireEye has seen them securely delete tools to hide their tracks. FireEye Intelligence has seen this threat group active since at least late 2015.
FireEye has installed a separate software programme in all computers of the BB. The software is being used to find out the path the hackers used to install the malware into the BB system.
The US company is continuously monitoring all computers.

 For all latest news, follow The Daily Star's Google News channel.
For all latest news, follow The Daily Star's Google News channel. 



Comments