Pegasus spyware: What is it and how does it work?
Previous Amnesty International Security Labs investigations unearthed evidence of Pegasus being installed on the phone of The Washington Post journalist Jamal Khashoggi's fiancée, Hatice Cengiz, just four days after he was killed in the Saudi Consulate in Istanbul in 2018. In another instance, for almost three years, Azerbaijan journalist Khadija Ismayilova's phone was regularly infected with the Israeli Pegasus spyware, giving "certain" governments direct access to her phone. After the recent investigative dig aided by The Washington Post and The Guardian, the first question that did our head in was a simple one: what is Pegasus?
Spyware has evolved leaps and bounds in the last decade. In 2010, one would have received a suspicious email, and only upon opening the email would the malware be installed in their computer. The initial version of Pegasus, however, adopted the "mobile-first" strategy, where targeted individuals would start to receive text messages which would look like their family members sending them a link to their bank accounts, or their location, etc. In January 2016, Carmen Aristegui, an investigative journalist in Mexico, started receiving messages with suspicious links after she published an investigation into property owned by former Mexican President Enrique Pena Nieto.
The updated Pegasus spyware is a "zero-link" technology which takes advantage of zero-day vulnerabilities -- meaning the user is not required to click on any link. Zero-day vulnerabilities are referred to as newly discovered vulnerabilities within the operating software, that the developer is still unaware of. Since the vulnerability is still in its "day zero", there are no patches or updates that can secure a user. Using such vulnerabilities, NSO Group -- the Israeli owner and creator of Pegasus -- sends the spyware to the target's phone, either through text message or a phone call. Since no action is required by the user, the malware instantly installs itself within the phone. Once installed, Pegasus gives NSO's "government clients" access to the target's device, bypassing even encrypted messaging apps like Signal, WhatsApp, and Telegram.
Since Pegasus hacks into the operating system, every activity within the phone can be monitored when the phone is switched on. It's as if someone is monitoring your phone activity over your shoulders. Pegasus operators can remotely record audio and video from your phone, extract phone messages, use GPS for location tracking, and recover passwords and authentication keys without the user even noticing. It's only when a device is sent for forensic screening, and experts look into the transfer of data to and from the phone, is when a potential attack can be confirmed. The dooming fact of it all is that since Pegasus exploits zero-day vulnerabilities, there is nothing that can be done regarding such breaches unless operating system developers proactively ship out an update to your phone, aimed to protect you from hi-tech malware like Pegasus.
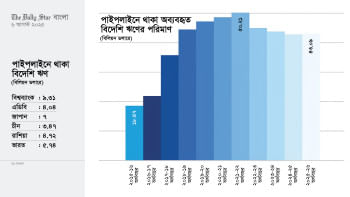
For years, activists and many heads of state have raised concerns about Israel's prominence in the surveillance sector, especially regarding private contracts made to different security agencies around the world with a questionable track record. The NSO Group believes all their government clients are democratic and heavily vetted. According to Haaretz, NSO clients include Saudi Arabia, Bahrain, Morocco, India, Mexico, Hungary, Azerbaijan to Togo and Rwanda.
There are hardly any legal limits on what Israeli surveillance and intelligence veterans can do after their service. IDF intelligence veterans take research ideas they worked on in the military and develop them in the private sector for profits. Israel's long occupation of the West Bank, Gaza, and East Jerusalem, coupled with its periodic wars -- as recently as the 11-day onslaught in May 2021 -- provides the perfect "laboratory for fine-tuning" different technological commodities that are created.

 For all latest news, follow The Daily Star's Google News channel.
For all latest news, follow The Daily Star's Google News channel. 


Comments